SCHNEIDER Modicon Quantum Safety PLC
Modicon Quantum Safety PLC is a safety programmable logic controller launched by Schneider Electric, which complies with the IEC 61508 standard and has a certification level of SIL3. Its core revolves around the implementation of safety functions, covering four dimensions: hardware configuration, programming specifications, communication mechanism, and fault diagnosis. It supports two deployment modes: independent/hot standby (HSBY), and ensures functional safety through dual processor execution, redundant I/O design, strict memory partitioning (safe/non restricted area), and dedicated programming software Unity Pro XLS. It is suitable for industrial safety scenarios such as emergency shutdown, burner management, and fire and gas monitoring. At the same time, it provides a complete verification and testing process and maintenance specifications to ensure that the system meets PFD/PFH index requirements in low/high demand modes.
1、 Document Fundamentals and Compliance
(1) Core information of the document
Document Name: Modicon Quantum Safety PLC Safety Reference Manual (Version 10/2017)
Applicable software: Unity Pro XLS V7.0 and above
Target users: Professional technicians with knowledge of functional safety and experience operating Unity Pro
Core objective: To standardize the hardware selection, programming, deployment, and maintenance process of SIL3 level security systems
(2) Compliance and Certification Standards
Standard Name Core Requirements Applicable Scenarios
IEC 61508 (2.0 version) SIL3 level, supports low/high demand mode for general industrial safety systems
IEC 61511 Safety Instrumented Systems (SIS) for Process Industries such as Chemical and Petroleum
EN 54 Fire Detection and Alarm System Fire and Gas Monitoring Scenarios
EN 298 Automatic Gas Burner Control System Burner Management
NFPA 85/86 Boiler Protection Standard Boiler Safety Control
2、 Hardware configuration and core features
(1) Secure CPU module
Model deployment mode core parameter fault detection mechanism
140CPU65160S independently deployed MTBF=600000 hours, supporting 8 secure I/O modules with dual processors (Pentium+application processor) for comparison and memory CRC verification
140CPU67160S hot standby deployment has the same parameters as the standalone version, supporting fiber link synchronization, automatic switching between primary and backup, and application consistency verification
(2) Safety I/O module
Module type, model, core characteristics, diagnostic function
Digital input 140SDI95300S, 32 points, 24Vdc, MTBF=900000 hours, disconnection detection, power monitoring, channel short circuit detection
Digital output 140SDO95300S 32 point, 24Vdc, MTBF=10000000h overload detection, circuit disconnection, timeout state configuration
Analog input 140SAI94000S 8-channel, 4-20mA, MTBF=700000 hours, over range detection, wire breakage detection, measurement linear verification
(3) Auxiliary hardware requirements
Power module: Only supports 140CPS12420 (AC redundancy) and 140CPS22400 (DC redundancy), requiring dual module deployment to ensure availability
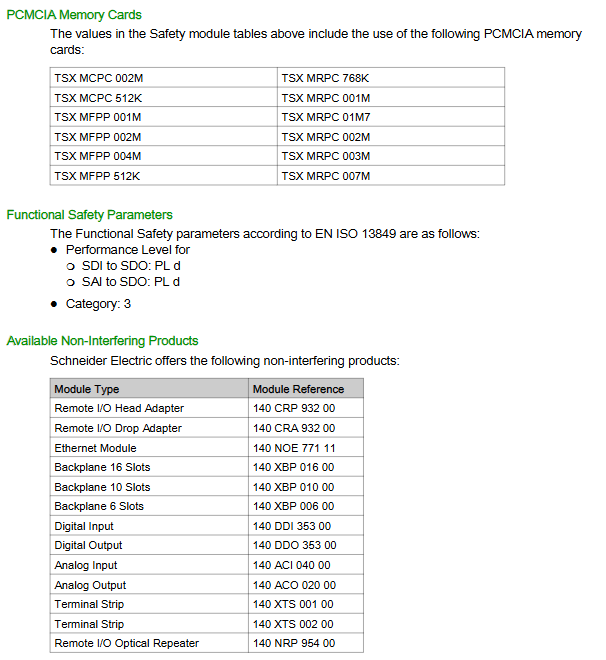
Non interfering modules: including backplane (140XBP series), Ethernet module (140NOE77111), remote I/O adapter (140CRP93200/140CRA93200), not involved in safety functions but must meet compatibility requirements
Wiring specifications: The digital output module needs to be connected in series with a 10A fast fuse, and the analog input needs to be shielded and grounded (recommended STB XSP3000 grounding kit)
3、 Programming standards and software operations
(1) Programming software and language limitations
Unique programming software: Unity Pro XLS (requires secure firmware support)
Language allowed: Function Block Diagram (FBD), Ladder Diagram (LD) only
Disable features: FAST/NTERRUPT tasks, jump statements, ST expressions, derived data types (DDT)
(2) Core programming requirements
Specific requirements and purposes for standardized categories
Task configuration only allows MAST tasks, with a minimum cycle of 20ms to ensure consistency in execution between dual CPUs
The data type only supports basic types such as BOOL/INT/FLOAT+simple arrays to avoid security risks caused by complex data structures
The use of function blocks only allows secure FFB libraries (such as S-AND_ * * *, S-DISIL2, etc.) to ensure the security of logical execution
Memory partition: secure area (write protected), unrestricted area (data transfer only through S2SMOVE-FB), isolated secure/non secure data
(3) Security protection mechanism
Application password: Protect project access, support permission grading (configuration/debugging/maintenance)
Auto lock: After 10 minutes of inactivity (default), the software will be locked and requires a password to unlock
Version stamping: Record the build time when generating binary files for version traceability
Project backup: Regular backup is required (recommended combination of full and incremental backup), with CRC checking for integrity
4、 Operation mode and fault handling
(1) Two operating modes
Mode core feature operation restrictions
Safe mode (default) executes safety functions, prohibits program modification of non downloadable programs, non mandatory variables, and non debuggable
Maintenance mode (temporary) allows program modification, variable forcing, debugging requires unlocking key switch+password, diagnostic results do not automatically execute security actions
(2) Fault diagnosis and handling
CPU failure: When a memory error/inconsistent execution is detected, it enters an error state, and all safety outputs are set to a safe state (power loss). It is necessary to power off and restart, and read the% SW125 error code
I/O module failure: When a channel fails, the single channel is set to a safe state. When a module fails, it automatically restarts and performs a power on self-test. If it fails three times, the module needs to be replaced
Communication failure: When the secure Ethernet communication timeout (configurable) occurs, the HEALTH position is 0, and the receiving end needs to trigger a security action
5、 Communication mechanism
(1) Communication types and restrictions
Core requirements for communication scenario support methods
PC-PLC communication Modbus TCP/RS485/USB requires Unity Pro XLS, verify application password
PLC-PLC communication security requires NTP time synchronization between Ethernet nodes, with unique ID parameters
PLC-HMI communication Modbus TCP/Modbus Plus only allows reading of secure data and writing to restricted non restricted areas
(2) Secure Ethernet point-to-point communication
Synchronization requirement: NTP server polling cycle of 20s, master-slave PLC time difference ≤ 2s
Configuration components: sender end s_WR-ETH FFB, receiver end s_RD-ETH FFB
Timeout configuration: SAFETY VNet ONTROL_TIMEOUT needs to be greater than 2 times (sending cycle+network delay+receiving cycle)
6、 Verification and maintenance
(1) Verification testing requirements
Verification cycle (PTI): up to 10 years, requiring full system testing to be performed in accordance with SIL3 requirements
Verification content: power cycling test, I/O channel verification, safety function triggering test
Document requirements: Keep verification records, fault logs, and project backup files
(2) Maintain standards
Module replacement: Supports hot swapping, and after replacement, a power on self-test (about 30 seconds) needs to be performed
Mandatory operation: Only maintenance mode is allowed, and operation logs need to be recorded and the mandatory operation should be lifted in a timely manner
Firmware upgrade: Only maintenance mode can be executed, and the hot standby system needs to upgrade the backup CPU first